Organizations no longer operate within four walls.
Neither should your cybersecurity stack.
Fully Managed
Advanced Cybersecurity
Antivirus software have become obsolete and are not enough to protect your organization.
Our security stack is available as a package or a-la-carte depending on your business’ specific needs.
Managed Endpoint Security
Upgrade your antivirus with Endpoint Detection and Resolution to anticipate and identify threats in real-time.
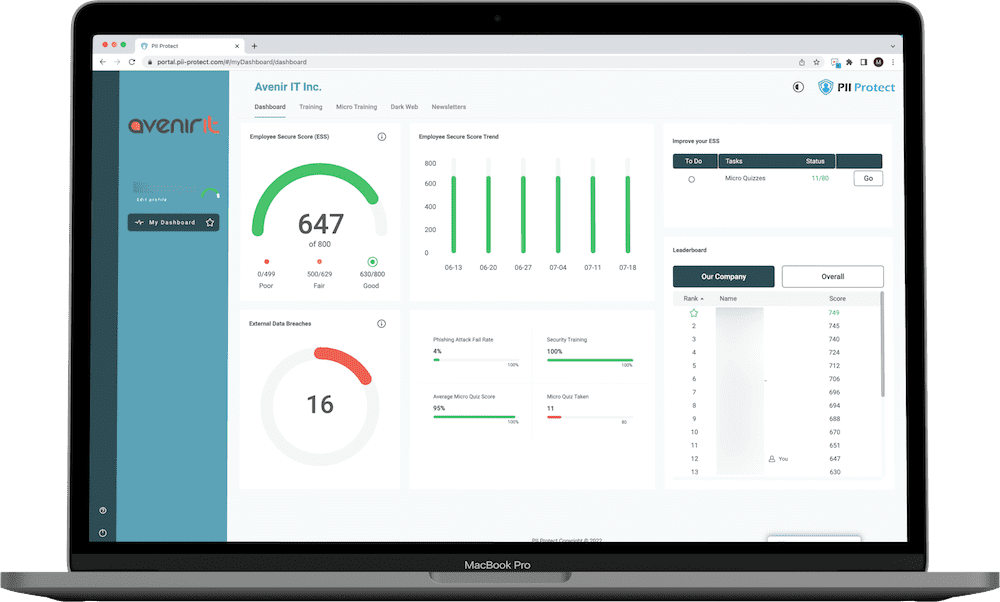
Online Cybersecurity Training
Gamify cybersecurity while creating human firewalls with fun educational tools.
Cloud to Cloud Backups
Prevent data loss caused by cyber attacks or human errors.
Cloud Firewall
Secure your remote and local staff with SASE and Zero Trust Network Access.
Simulated Phish Testing
Get insights in your team's ability to catch fake phishing emails.
3rd Party Cybersecurity Testing
Receive bi-annual pen testing to highlight potential risk areas.
Web Content Filtering
Increase profits preventing access to time wasting or malicious websites.
Dark Web Monitoring
Be notified if your business and staff may have been part of a data leak.
Single Pane of Glass
Our SIEM solution will analyze data from multiple sources to deliver insights from known and unknown threats.
